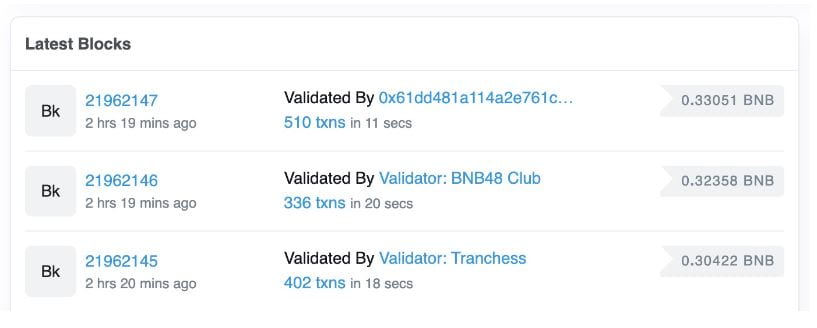
The BNB Chain developed by the cryptocurrency exchange Binance was hacked in the early morning of the 7th! The official cross-chain bridge (BSC Token Hub) was stolen by hackers, and the loss amounted to hundreds of millions of dollars. According to BscScan data, the chain has suspended block production (the last block was 6 points).
Binance founder CZ also urgently stepped forward to emphasize the safety of user funds, and the details of the attack are under investigation:
We have asked all validators to suspend BSC for additional BNB resulting from cross-chain bridge BSC Token Hub utilization. Questions are included. Your funds are safe. We apologize for the inconvenience and provide further updates.
The hack caused a lose of over $700 million?
Due to the recent incident, the total amount of damages has not been determined. According to community analysis, the attackers are suspected of stealing 2 million BNB (about $570 million at the current price), about $80 million in ETH and other assets, and tens of millions of assets transferred to other chains. Youchain analysts estimated the maximum loss to be $718 million.
According to DeBank data, the wallets marked as attackers had $540 million in assets at the time of writing.
However, CZ, the founder of Binance, tweeted that the total loss of the attack was about 100 million US dollars, which was very different from the results of the chain data, and it has yet to be clarified.
BNB slumps 5% in seconds
At the same time, in terms of BNB price, as soon as the news of the attack was made public, BNB fell by nearly 5% within 2 hours, but it has rebounded before the deadline, and is now at $286.3.